RackTop's ImmutaVault™
Immutable cyber vaulting technology enables an active airgap for your production data
Introducing RackTop’s Cyber Vault Technology
Cyber vaulting with BrickStor SP for guaranteed security, optimized workflow, and uncompromised validation
RackTop BrickStor’s ImmutaVault feature is a secure virtual air gap that provides guaranteed isolation and immutability for critical production data as well as real-time active defense against cyber threats. With RackTop’s patented technology, your organization’s data is safeguarded with protections that are like a physical air gap but without the need to physically disconnect network cables to maintain security. ImmutaVault reduces your threat window by optimizing your workflow with faster and more frequent data transfers, eliminating the risk or compromise that comes with a traditionally connected system. Vaults are protected from rogue admins through RackTop’s unique data ownership and privilege management scheme, and compliance is simple with one-click data integrity checking, cryptographic validation of vault contents, and source system chain of custody. RackTop’s ImmuaVault is a quick and easy step to guaranteeing data availability in the event of a cyber attack.
Features
Active Air Gap
Through RackTop’s patented technology, your data will be protected to the same level as a physical air gap without the need for disconnecting network cables or separate systems. Strong isolation and immutability ensure data is only accessible when exposed through a view that is managed by the assigned vault owner(s).
Protection from Privileged User Abuse
Vaults are protected from admin or operator abuse (insider threat, misuse of privilege to view data) and accidental or early destruction. The isolation system ensures vaulted data is only accessible to its owners.
Data Attestation
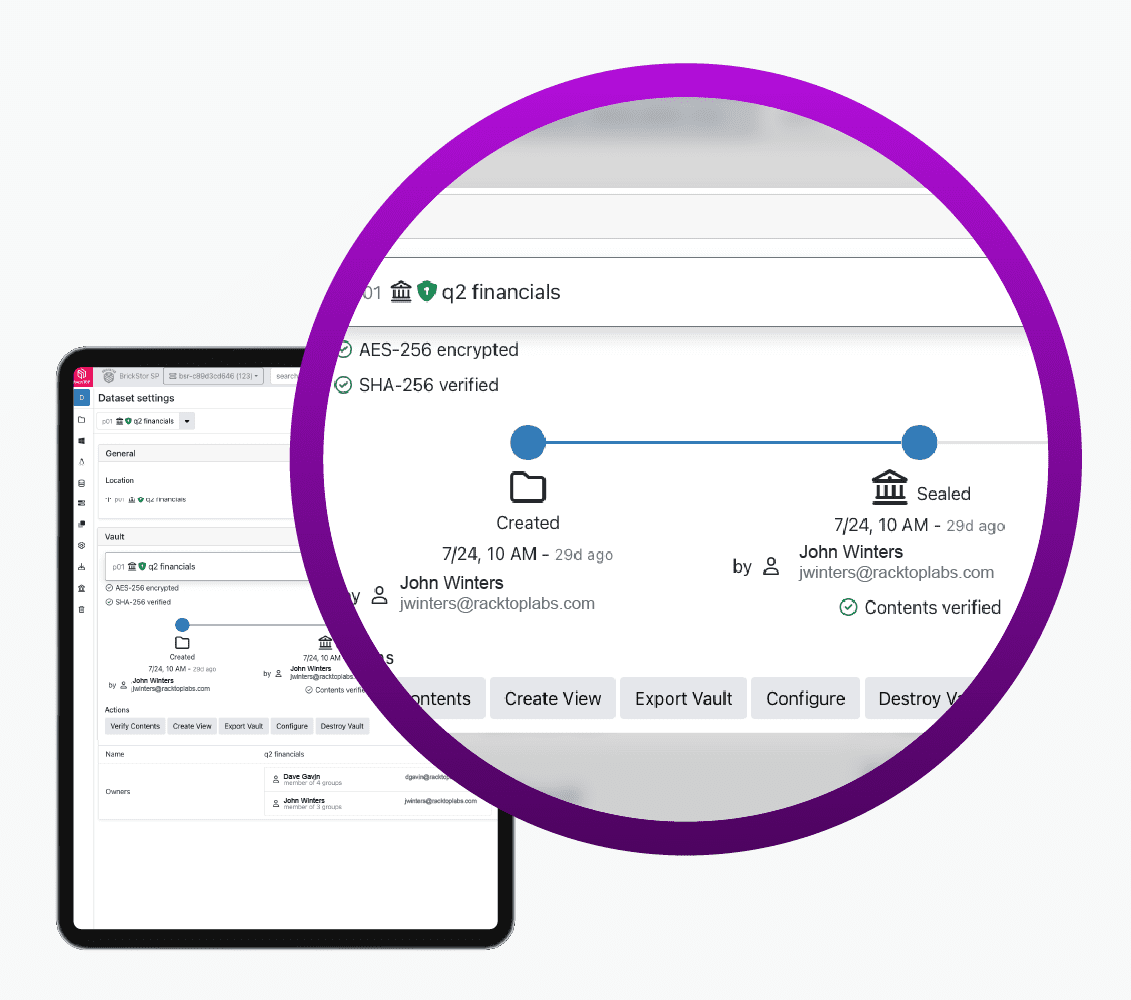
Data stored in a vault can be cryptographically verified, without being exposed to a user or auditor, to ensure the data
integrity from the time of ingest into the vault up to any point in the future.
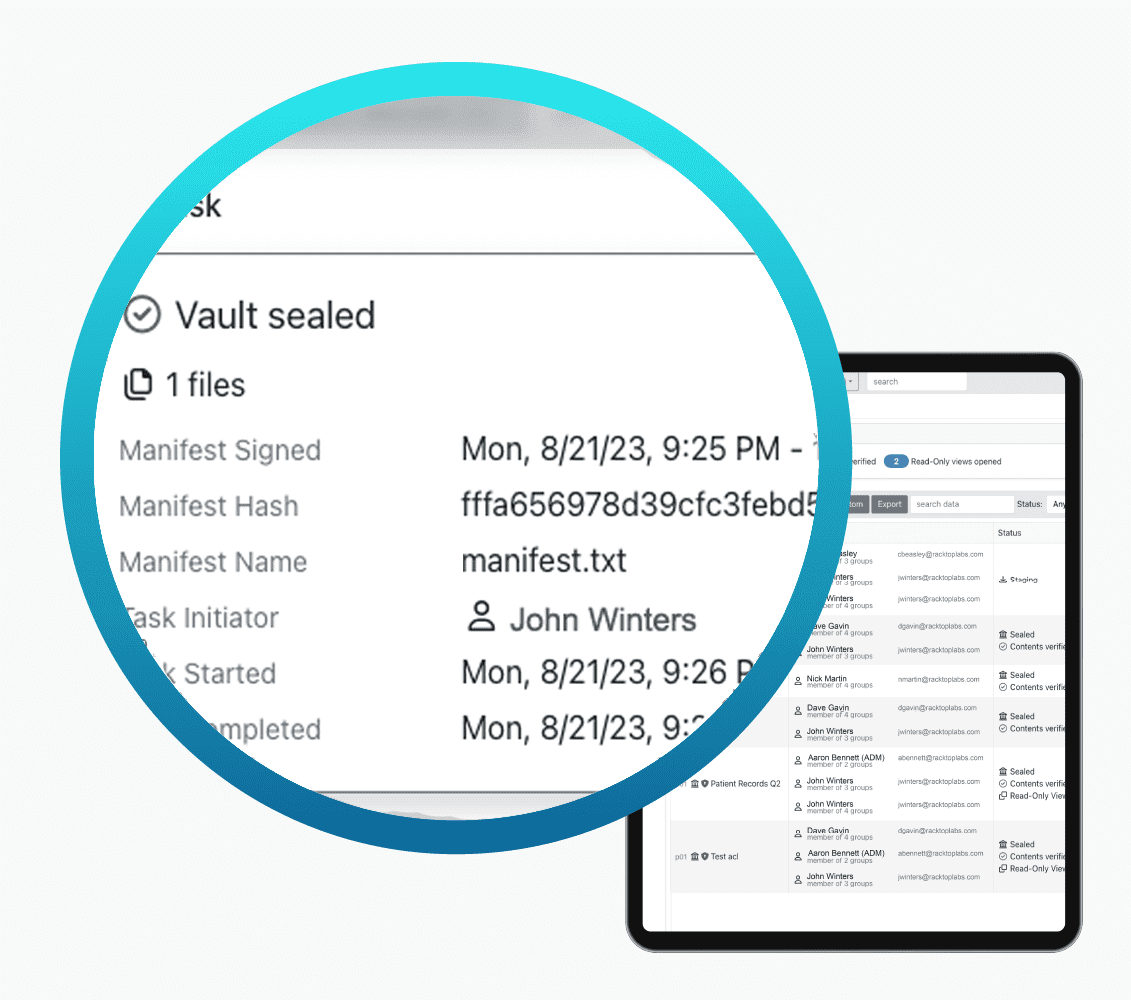
One Way and Permanent
Vaults are permanently protected with no mechanism to modify, add, or revert once sealed, validated, and cryptographically signed. This true immutability protects from outsiders, insiders and advanced system (OS) oriented attacks.
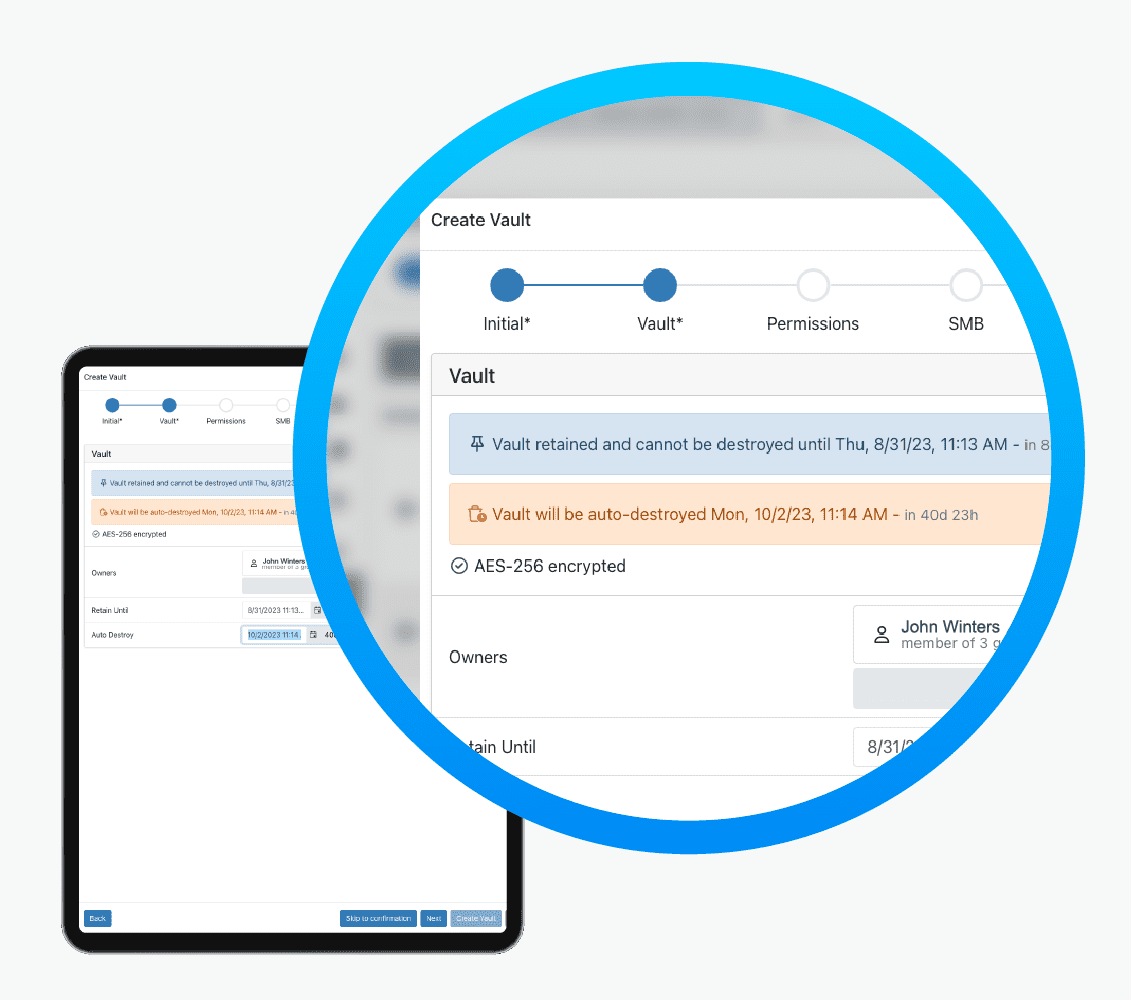
Policy Driven
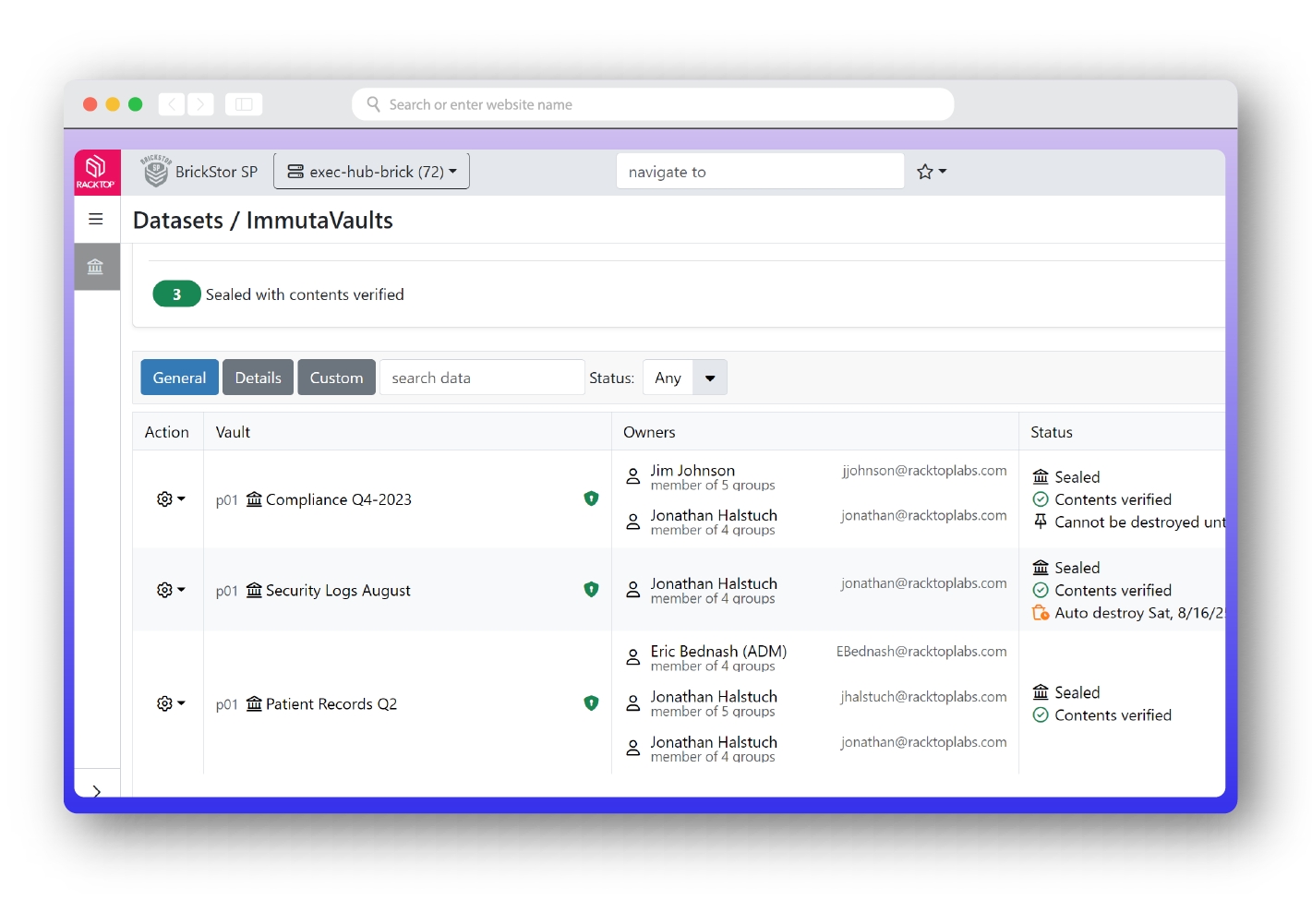
Each vault implements its own policy which dictates the data owner (who can view and share vaulted data), as well as the retention and protection settings required to meet any type of regulatory or security compliance requirement.
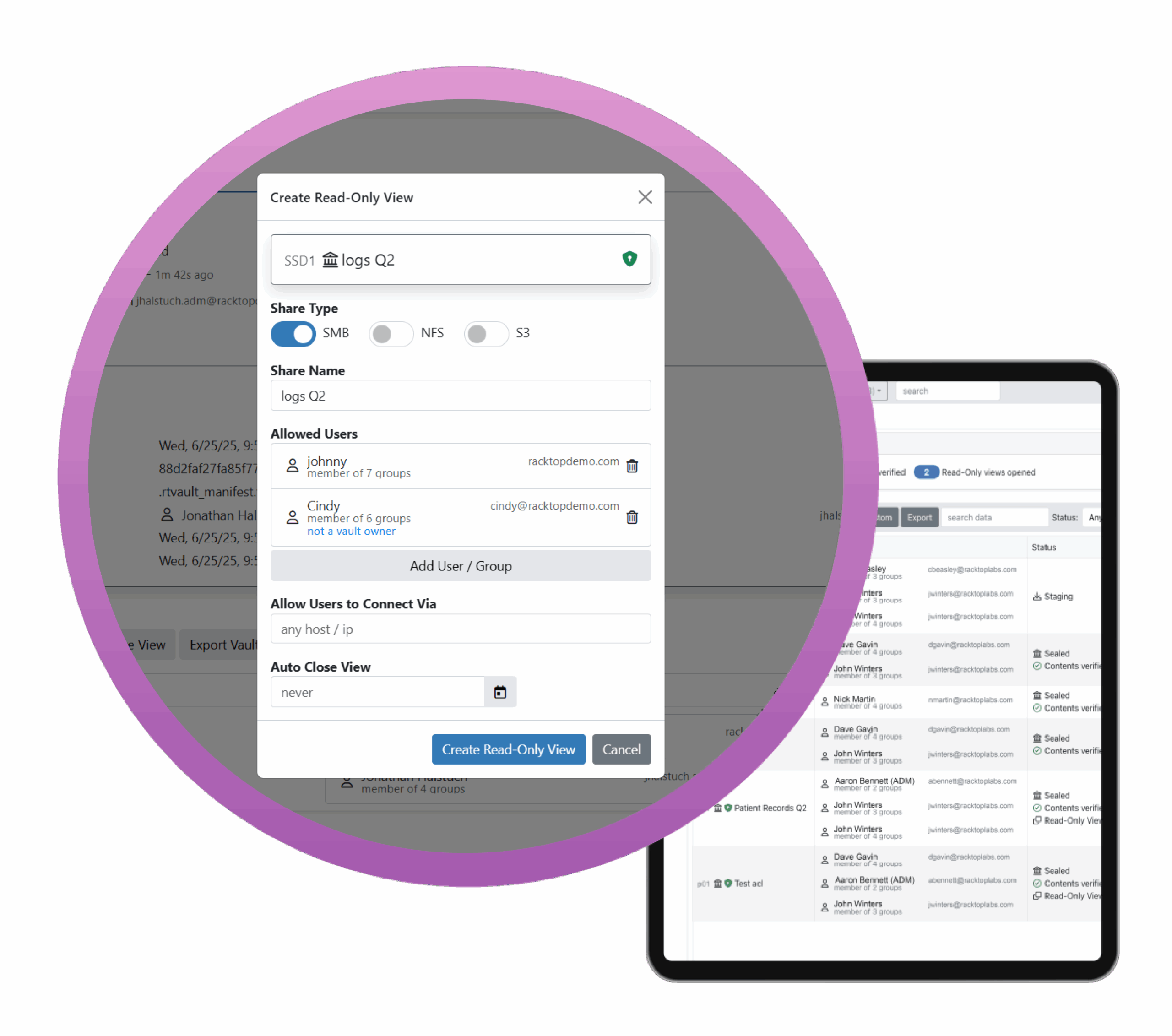
Secure View and Digital Twins
Once a vault is sealed, the only way to access its contents is through a view via RackTop’s digital twin technology. Data owners can instantly “twin” an existing vault and share it over common network protocols like NFS and SMB to a targeted set of users, groups, or systems. The original vault data is never accessed. Only the digital twin, which is an instant zero-copy clone of the vault’s data, is available to be accessed. Vault views are governed by policy as well, so vaulted data can be exposed for any length desired and only to users, hosts, and networks associated with that twin’s view.
Chain of Custody
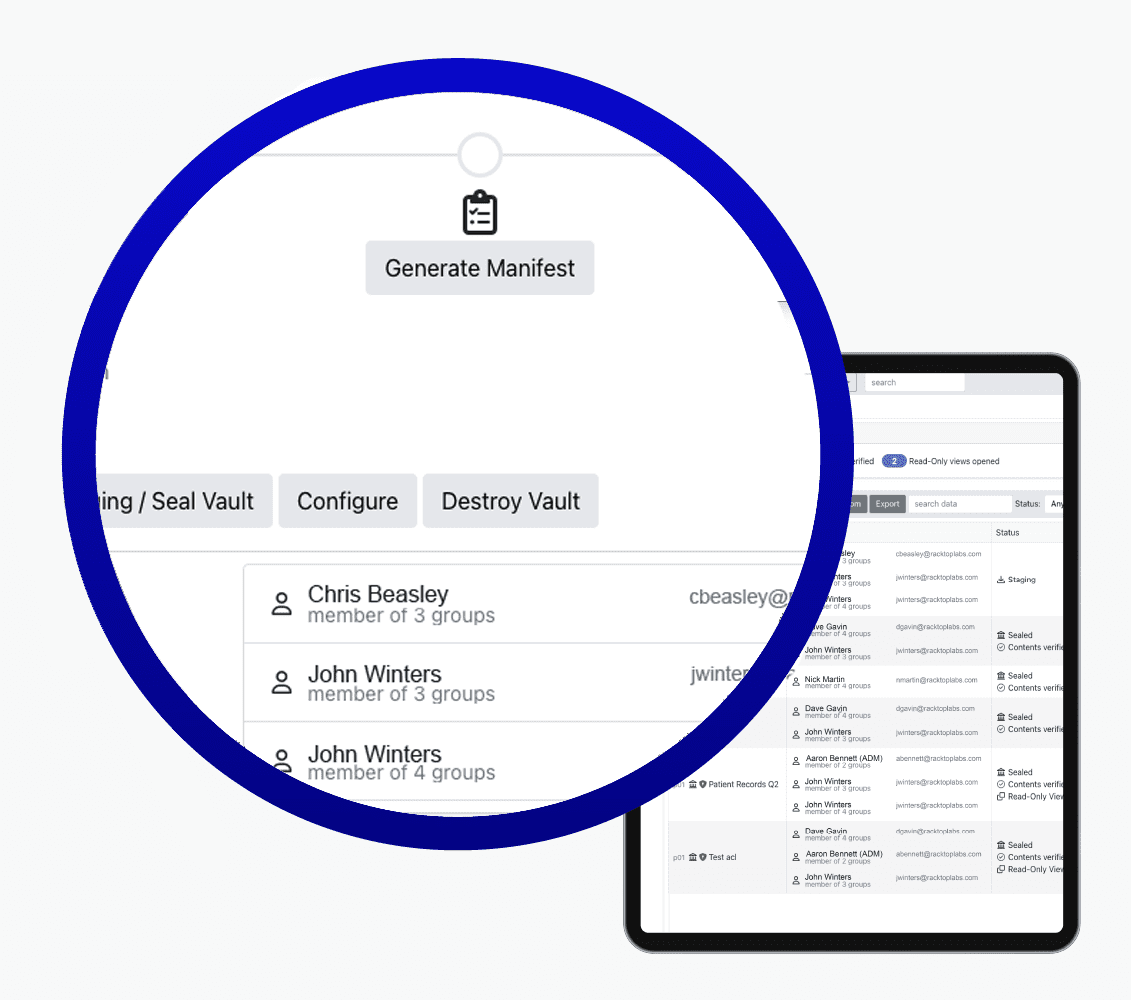
Data provenance through user behavior activity auditing and the vault’s cryptographic manifest provide a complete chain of custody for data through ingest, disposition, and destruction. Vaults can only ingest data from users, applications or source machines that are identified as data owners. The entire data ingest process is audited and verified, and when combined with the data provides the chain of custody proof required for the most critical data and most secure environments.
Common Protocols
Vaults in the staging phase, prior to sealing, can ingest data from any source that can mount and NFS or SMB file share. Another unique benefit of RackTop’s LiveVault is that data being used in production can be instantly converted into a vault without the need to copy it to a new system, which saves on time, money, and additional storage costs.
Here’s how it works
ImmutaVault for BrickStor
ImmutaVault is available in BrickStor version 23.6 and newer. The feature is a cyber vaulting technology that provides guaranteed isolation and immutability for critical production data. It’s applicable in compliance use cases as well as for cyber recovery into an air gapped clean room.
The solution provides a virtual air gap capability to provide protections and controls that are similar to a physical air gap, but without the need to physically disconnect cables. This enables more frequent data transfers and rapid access to data when its needed. Watch the demo to see how to perform several common operations.
ImmutaVault reduces the complexity of building isolated recovery environments to protect critical data
Contact
Phone: +1 443-276-6973
Email: RackTop info
Support: Customer log-in
Address: 8170 Maple Lawn Blvd. Ste. 180
Fulton, MD 20759 USA
Sign-up for solution updates